How to Spot Common Cyber Scams
In 2016, some 15.4 million consumers were victims of identity theft or fraud – up 16% from 2015.[1] With cyber crime continuing to rise and cyber criminals becoming increasingly sophisticated, it’s important to understand common cyber scams and how to avoid them. Here are three common cyber scams and tips for recognizing them.

Inbox Scams
Phishing and scam emails are becoming harder to spot and more frequent. Malicious scam emails try to trick you into installing viruses on your computer – it’s important to not click any links or open any attachments. Tips for recognizing inbox scams include:
- Bad grammar, typos, and/or unnatural syntax
- Lack of or improper use of official letterhead and/or logos
- Missing approval footers
- Broken or badly formatted images
- Empty threats
- Instructions to click a link or verify and/or reactivate accounts
- Demands for passwords and/or other sensitive information
Some legitimate emails can sometimes contain two of the above items such as a typo and improper use of logos. Emails that include many, if not all, of these mistakes are potential scams.
[You Might Also Like: Infographic - "6 Common Types of Cyber Attacks"]
Fraudulent emails have been sent out claiming to be from PayPal. The official looking message sent by scammers attempts to get the recipient to click on a malicious link. The email begins by warning the recipient that someone is using their PayPal account without their knowledge, claiming that there has been recent activity on their account from a suspicious location. The email request the recipient to click on a link to login and confirm their account. Below is an example of what the email looks like:
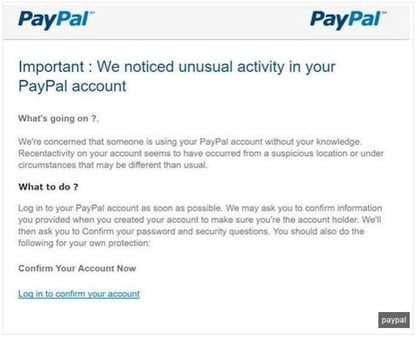
In this example, if the recipient clicked on the link in the email it would take them to a fake login site that was built to steal user’s credentials and security answers.
Inbox Scam Takeaways & Red Flags
Ensure all employees are wary of any email containing an attachment they aren’t expecting. Before clicking on anything, confirm with the sender via phone, text, or separate email what it is before opening or clicking anything.
An email from a retailer is probably suspicious if the recipient hasn’t made a recent purchase. Employees who receive this type of email should be instructed not to click anything. Instead, they should type the URL into a browser, login to their account, and check for notifications there.
Missing sender or recipient information, generic greetings, misspelled email addresses (i.e. billing@paipal.com), and email addresses that don’t match the company name should be cause for concern of malicious activity. Any emails that ask the recipient to download a form or complete a task are highly suspicious. All suspicious emails should be reported to IT.
[You Might Also Like: Blog Article - "How to Prevent Common Cyber Attacks"]
Malicious Websites & Malvertising
Malicious websites are designed to look like a page or ad on a legitimate website, and these sites can look incredibly real. Cyber criminals typically utilize branding and logos, which is why users may easily fall victim and give cyber criminals their personal information or access to install malware onto their systems. To accomplish the redirect to a malicious site, hackers insert code into a legitimate site which redirects unsuspecting users to their malicious site. Tips for recognizing malicious websites and Malvertising include:
- Poor spelling, unprofessional imagery, and bad grammar
- Links that redirect to a different domain
- Misspelled URLs
- URLs with unusual domain extensions
- Unsecured sites that start with “http” – all secure sites start with “https://”
Malvertising increased by 132% in 2016 over 2015[2]. The increased sophistication of programmatic advertising technology has introduced powerful, highly accurate profiling capabilities which cyber criminals leverage across every link in the advertising delivery chain to target precise groups of users. Here is an example of a malicious page:
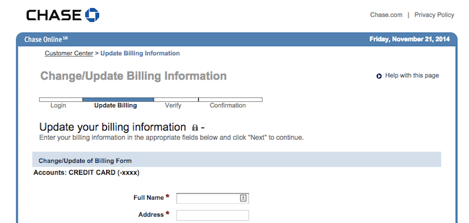
In this example, cyber criminals created a malicious page that was designed to look like a page on Chase Bank’s website to collect user information.
Malicious Websites & Malvertising Takeaways & Red Flags
Educate employees about the risk and practice safe browsing habits, making sure they are accessing sites using the HTTPS secure communication protocol and being skeptical of any site asking for private information. Train employees how to check URLs that links point to – hover your mouse over the link to reveal the complete URL in the status bar at the bottom of the browser.
Pop up Scams
A fake pop up is a form of Internet fraud that implements social engineering and fear tactics to get the user to take the action the cyber criminal is requesting. Fake pop ups are designed to extort the victim to get their money as well as installing malware to gain access to personal information. Tips for recognizing a fake pop up include:
- Poor spelling, unprofessional imagery, and bad grammar
- Links that redirect to a different domain
- Misspelled URLs
- URLs with unusual domain extensions
- Pop ups that require you to enter personal information
One common pop up scam is your web browser being redirected to sites that display tech support alerts, asking you to call a support number to fix your device. These fake tech support alerts are shown in a way that trick the user into thinking their computer has crashed or that a virus has been detected on the computer. The message displayed attempts to scare the infected user into calling one of the listed numbers to receive support. If the number is called, the person on the other end will try to sell the victim unneeded support contracts and services. The scammer may attempt to get the victim to allow remote access into their computer, and that’s when personal information is stolen. Here is an example of a pop up scam:
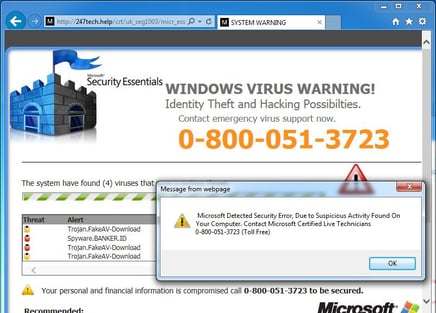
In this example, a pop up was generated appearing to be from Microsoft stating that the user’s computer has a virus. The user was instructed to call a number to get the error corrected.
[You Might Also Like: Infographic - "10 Ways to Protect Your Computers from Malware"]
Pop up Scam Takeaways & Red Flags
Companies will never send unsolicited email messages or make unsolicited phone calls to request personal or financial information or fix your computer. Treat all unsolicited phone calls or pop ups with skepticism and never provide your personal information.
Online scams are constantly evolving and cyber criminals are becoming increasingly savvy in using methods to get information and money from unsuspecting people. Arming yourself and your employees with knowledge on how to protect your identity is key to avoid falling victim to scammers.
[1] https://www.riskiq.com/infographic/riskiqs-2016-malvertising-report/ [2] https://www.cnbc.com/2017/02/01/consumers-lost-more-than-16b-to-fraud-and-identity-theft-last-year.html
